Computer Plug-in
The Computer plug-in is used to work with local computer′s file system. It can be used as both source of data and storage destination.
Files and folders of the plug-in file system correspond to common files and folders. They support all attributes, such as file size, creation time, modification time, and other.
Prerequisites
The plug-in can back up open files, i.e. files that are locked by other applications. This is made with the use of the Volume Shadow Copy Service. If you want to back up open files, then you need to have this service running on your system.
Using Computer Plug-in as Data Source
The Computer plug-in is the main way to back up local files and folders.
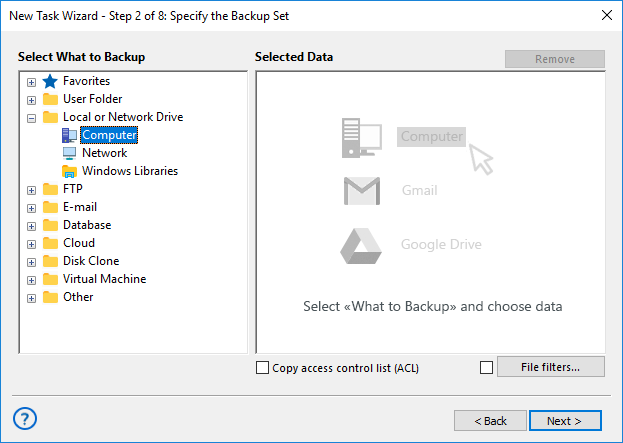
To add data to backup set, follow these steps:
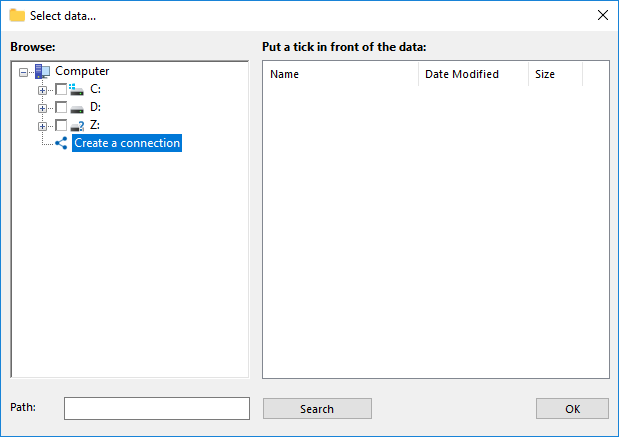
- In the Data Sources pane, click Computer in the Local or network drive group. The Select data... dialog will open.
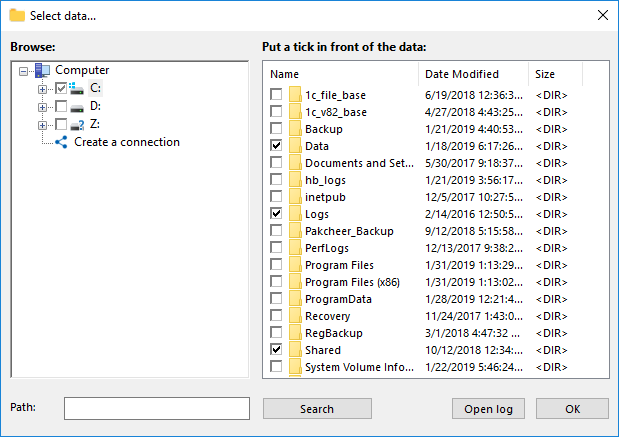
- Check the boxes next to files and folders that you want to back up.
- When finished the selection, click OK. Selected data appears in the Backup Set pane of the New Task Wizard.
You can find more information about selecting data for backup in the Specify Backup Set chapter.
Using Computer Plug-in as Destination
Using the Computer plug-in as storage (i.e. copying backups to a local folder) is made in a very straightforward way. After selecting data for backup, you need to select destination.
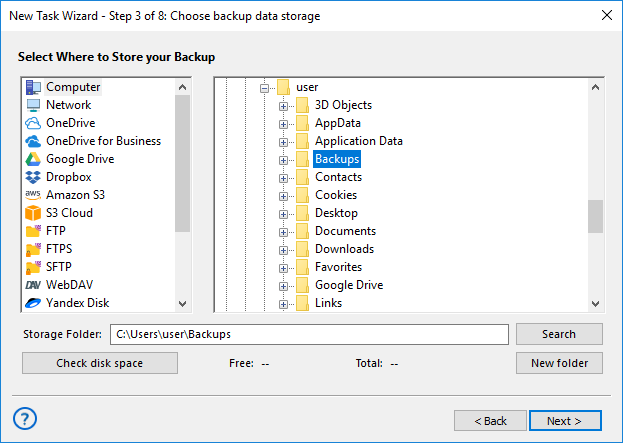
To select a local destination, follow these steps:
- In the Storage Destinations pane, select Computer. Your local file system is displayed in the Folder Selection pane.
- In the Folder Selection pane, browse for a target folder.
- Click Next.
You can read general description of this step of the New Task Wizard in the Select Destination chapter.
Using Computer Plug-in in Restore Tasks
General scheme of restore task creation is as follows:
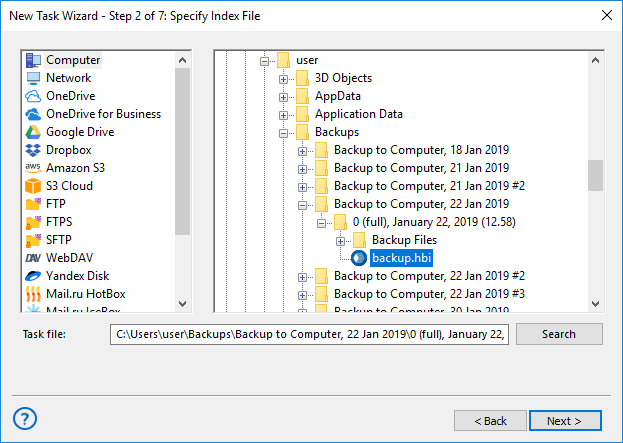
- Open New Task Wizard.
- Select Restore task, and then click Next.
- Browse for the index file (backup.hbi). If your backups are located in a local file system, then you need to select Computer in the Storage Destinations pane to the left, and browse for the index file in the Index File Selection pane to the right. Click Next.
- If you are restoring backups of local files and folders, default path of restoration will have the Computer plug-in.
If you want to restore your files to a different folder, follow these steps:
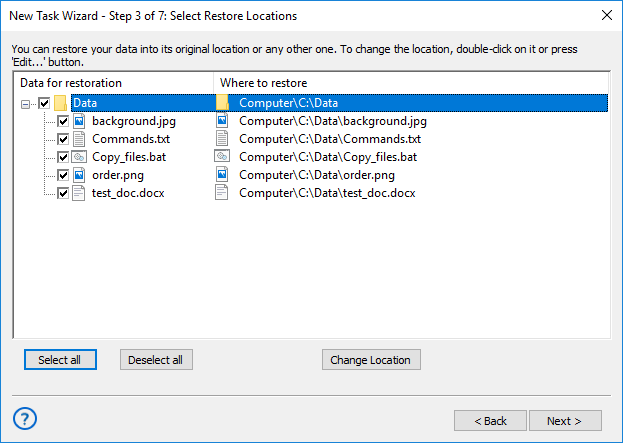
- 4.1. In the Select Restore Locations dialog, select a file or a folder, and then click Change Location. The Change restore location dialog opens.
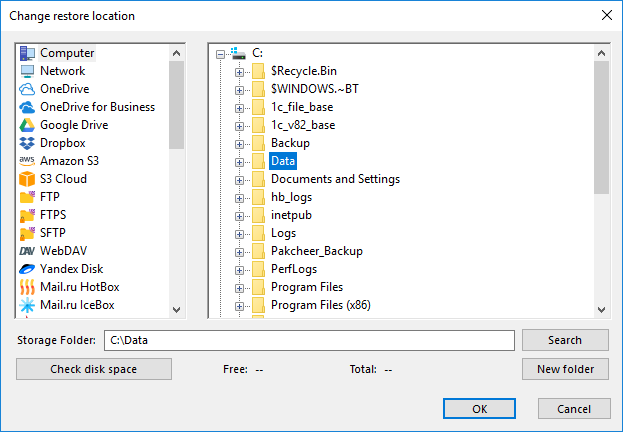
- 4.2. In the Change restore location dialog you can also select other file systems than the one provided by the Computer plug-in, e.g. FTP or WebDAV. Select a new location, and then click OK.
After verifying paths of restoration, you need to select type of restoration, enter decryption password (optional), and name the task. These steps are not specific to the Computer plug-in. To learn more, please see Restore Task.
Mounting a Protected NAS Unit via the Computer Plug-in
To use a mapped drive on a NAS unit protected by password, you can mount its drive via the Computer plug-in, as described in the next instruction.
- On Step 2 or 3, select Create a connection on the right panel of the Computer plug-in.
- In the dialog window, please enter the connection parameters:
- Connection Title: Any name that you want to assign to this connection.
- NAS address: Network drive address on the network.
- Login: A user login to a protected NAS.
- Password: A corresponding user password to this NAS unit.
- Local drive: A letter that Handy Backup must assign to a NAS drive as a mapped disk.
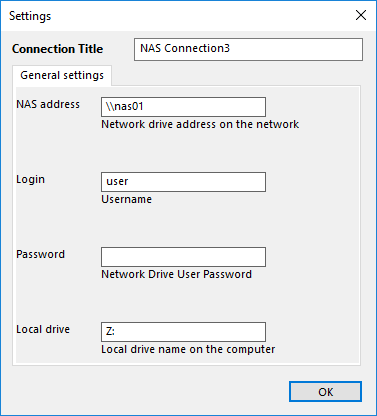
- Click OK. Handy Backup will mount a NAS protected drive as a mapped disk.
- Now you can see the drive in the My Computer section of a file system list.
You can use this mapped drive as usual storage device.
Note: The program will unmount a drive automatically after finishing a task wizard. Starting from this point, Handy Backup will mount a drive every time before executing this particular task, and unmount it after finishing a task. This approach adds to security of protected data.
Contents: